Vecteur Stock Internet Security, cyber security, fingerprint scanner, face recognition, password phishing, icons Infographic design template. Creative concept with 5 steps | Adobe Stock
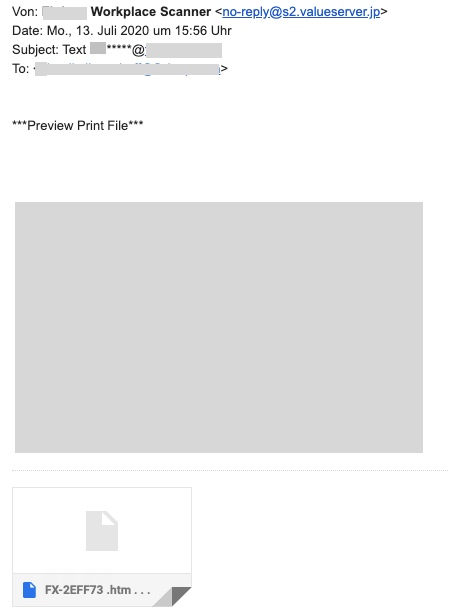
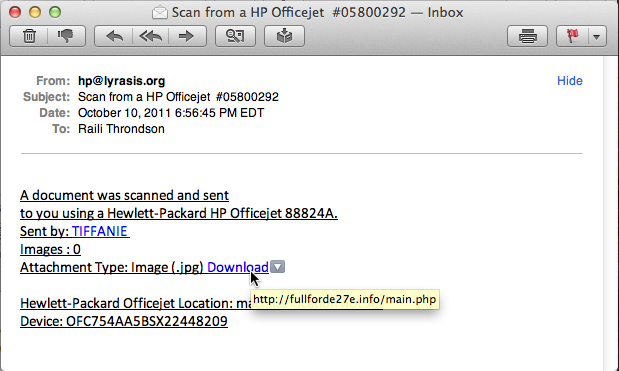
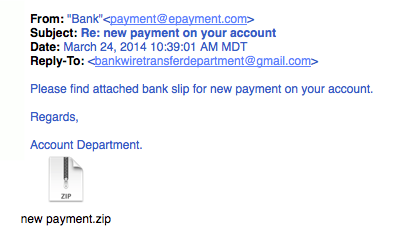
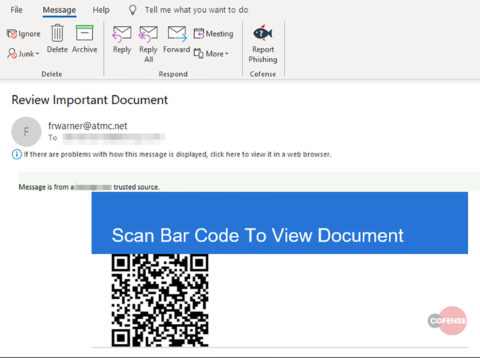
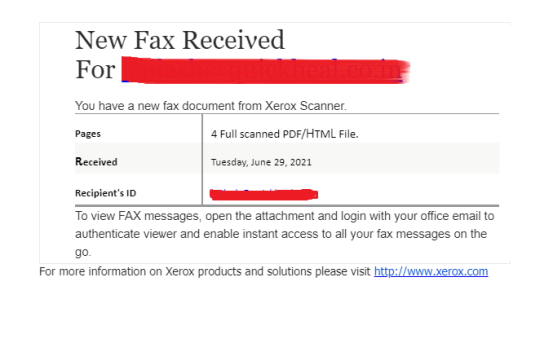
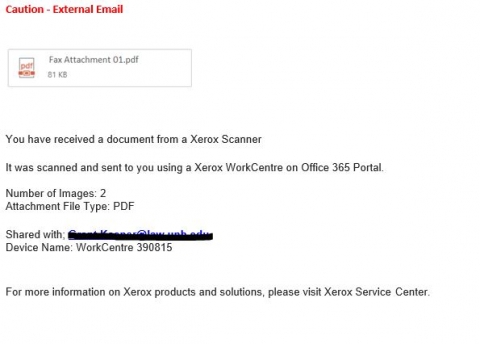
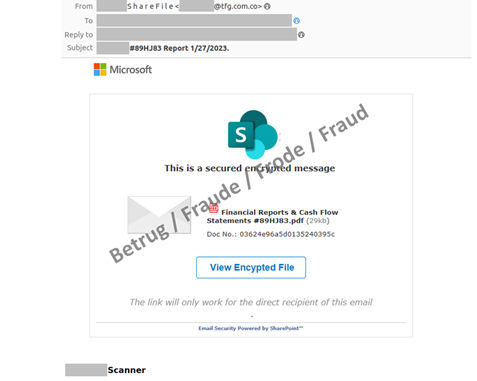
Analysis of a phishing email. As the whole world has become more used… | by Laur Telliskivi | Medium